Home Security and IoT Devices
 We connect more and more devices to the internet in our homes every day. The number has increased exponentially over the last ten years. Homes now typically have 10.37 devices connected to the internet. Mobile devices and PCs represent a little over half of those connected, and the rest are IoT devices.
We connect more and more devices to the internet in our homes every day. The number has increased exponentially over the last ten years. Homes now typically have 10.37 devices connected to the internet. Mobile devices and PCs represent a little over half of those connected, and the rest are IoT devices.
IoT stands for Internet of Things. The term is used for any other type of “smart device” that connects online. Home IoT devices can be everything from your streaming stick to the smart refrigerator. Smart baby monitors and Alexa voice assistants are also examples of IoT.
Another change snuck up on us over the last couple of years. The increase in remote and hybrid work profoundly impacted the world. The pandemic itself caused a major shift in where we work, flipping the standard office paradigm on its head.
As of now, working remotely has become the norm for many companies around the world. This change has created conflict with and put increased scrutiny on the security of all those IoT devices. Those Echo pods frequently now share a Wi-Fi network with business data and devices.
Two alarming statistics should grab our attention, illustrating the issue with IoT security:
- Over the first six months of 2021, the number of IoT cyberattacks skyrocketed by 135% over the level of the prior year.
- An estimated greater than 25% of cyberattacks against businesses involve IoT devices
Hackers Use IoT Devices to Network With Computers & Smartphones
Smart devices represent a risk to every other device on any given network. These IoT devices are typically easier to breach than PCs or phones. So, hackers will happily use them as the gateway into other devices sharing the same network.
A criminal probably doesn’t care about the shopping list stored in the smart refrigerator. However, they’ll happily breach that fridge to access other devices are on the same network.
The hacker can then exploit the sharing and permissions often present on home networks. Through these protocols, they gain access to your work computer or mobile device. These devices hold important business data and access to identity details.
Why are IoT devices less secure than computers and smartphones? Consider a few reasons:
- They usually don’t have antivirus or anti-malware capabilities
- Users often don’t update IoT devices often enough
- They provide basic interfaces which can hide a breach of the device
- People often don’t know to change the default device username and password.
- Sharing household settings on IoT devices makes them easier to hack
Improve Security By Putting All IoT On A Separate Wi-Fi Network
Nearly all modern routers provide the ability to set up a second Wi-Fi network, usually called a “guest network.” This alternate network shows up when you connect to Wi-Fi as a separate Wi-Fi network which a device can use to get online.
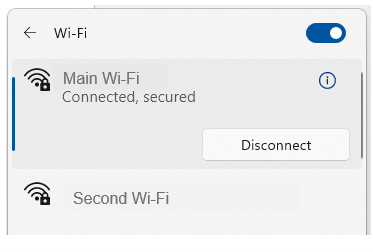
By connecting all your IoT devices through a separate network you improve security. Doing so cuts that bridge that hackers can use to wiggle in through an IoT device to get to another device on the same network. They’re looking for those that hold sensitive information (computers and mobile devices).
In fact, when you separate those two categories (IoT devices and sensitive-info devices) onto different networks a hacker can only see one network. When they breach one of your smart devices, they can’t tell you have a PC or smartphone. They can’t see the other network.
This represents an important layer of security. Regardless of whether you’re a remote worker or simply using your home computer for personal budgeting and banking, it can help. Every PC and smartphone usually contains access to online banking or personal information.
Here’s the step by step procedure to separate your IoT devices.
- Step 1: Log into your router settings.
- Step 2: Search the settings for an area that allows you to set up a guest network. This will be different for each router, so you may need to access a help guide online.
- Step 3: Create the guest network according to the router prompts. Make sure to use a strong password.
- Step 4: Change the password for your existing network. This keeps IoT devices from automatically reconnecting to it.
- Step 5: Connect all IoT devices in your home to the new guest network.
- Step 6: Reconnect your sensitive devices (computers, smartphones) to the preexisting network using the new password
As you add new devices to your home, make sure to connect them to the appropriate network. If it’s a PC, smartphone, or tablet, do it on that network. If it’s an IoT device, use that network. This keeps the layer of security effective.
One more tip: When naming your Wi-Fi networks, don’t use descriptive names that are easy for just anyone to understand. This includes things like “IoT network” or your name, address, or router model name.
It’s best to use names that won’t give the hackers valuable information they can use in attacks. Use things out of your fandoms, the author of this article is thinking of Game of Thrones references for her nex
Why Is This Published By A Business Phone Company?
Here at NoContractVoIP, we believe that your success is our success. To get the latest helpful content delivered to your inbox every month, subscribe to our newsletter here.
Looking for the finest stress-free custom business telephone systems? Contact us or call today at 866-550-0005!
